Once you have a grasp of the basics, start exploring the various types of cryptocurrency wallets available.
Introduction:
Following on from last weeks article which covered Understanding the Basics of Cryptocurrency Wallets, this weeks article (the second part of our three part series - Read part 1) will cover Types of Cryptocurrency Wallets. It is careful to note that there are a multitude of Crypto Wallets and an enormous amount of best practices to follow but this article hopes to give you an overview and cover the most important aspects.
II. Types of Cryptocurrency Wallets
Once you have a grasp of the basics, it’s essential to explore the various types of cryptocurrency wallets available:
2.1 Software Wallets
• Overview of software wallets.
Software wallets, also known as digital wallets, are a category of cryptocurrency wallets that exist as software applications or programs designed to run on various devices, including computers, smartphones, and tablets. They are one of the most accessible and widely used types of cryptocurrency wallets due to their user-friendly interfaces and convenience. Software wallets come in various forms, including online wallets (which are web-based and require an internet connection), desktop wallets (installed on a computer and accessible offline), and mobile wallets (designed for smartphones and tablets, offering mobility for on-the-go transactions). These wallets allow users to generate and store their public and private keys, making them versatile tools for sending, receiving, and managing cryptocurrencies. While they offer convenience and accessibility, users must exercise caution, as they are connected to the internet, making them susceptible to online threats and cyberattacks. Proper security measures, such as using strong passwords and keeping software up-to-date, are essential when using software wallets to ensure the safety of one's cryptocurrency holdings.

• Pros and cons of using software wallets.
Using software wallets for cryptocurrency storage has its pros and cons. On the positive side, software wallets are highly accessible and user-friendly, making them an excellent choice for individuals new to the world of cryptocurrencies. They offer convenience, allowing users to access their funds from various devices and locations, providing flexibility for everyday transactions. Additionally, many software wallets have intuitive interfaces that simplify the process of sending and receiving cryptocurrencies. However, there are also drawbacks to consider. Software wallets are connected to the internet, which exposes them to potential online threats, including hacking, malware, and phishing attacks. Users must take extra precautions to safeguard their private keys and ensure the security of their wallet, which can be challenging for those less experienced with cybersecurity. In summary, software wallets provide accessibility and ease of use, but users should be diligent about security to mitigate the inherent risks of online exposure.
• Examples of popular software wallets.
Several popular software wallets cater to a wide range of cryptocurrency users. One of the most well-known options is Coinbase, which offers both online and mobile wallets with a user-friendly interface, making it an excellent choice for beginners. Exodus is another popular software wallet known for its sleek design and multi-currency support, providing users with a diverse range of cryptocurrencies to manage in one place. Electrum stands out for its security features and compatibility with hardware wallets, making it a preferred choice for more advanced users who prioritize safety. MyEtherWallet (MEW) is designed specifically for Ethereum and ERC-20 tokens, offering a web-based platform that allows users to interact with the Ethereum blockchain securely. These examples showcase the diversity of software wallets available, catering to different preferences and needs within the cryptocurrency community.
:max_bytes(150000):strip_icc()/Crypto_Wallets_Review-0cfaf508fdaa42aaa8f5a9563e45300b.jpg)
2.2 Hardware Wallets
• Explanation of hardware wallets.
Hardware wallets are specialized devices designed for the secure storage and management of cryptocurrencies. They are often considered one of the most secure options for safeguarding digital assets. Unlike software wallets, hardware wallets store the user's private keys in a physical, tamper-proof device, making it nearly immune to online threats such as hacking, malware, or phishing attacks. These devices typically have a small screen and buttons for user interaction, enabling the signing of transactions directly on the device. Hardware wallets are known for their "cold storage" capability, as they can be disconnected from the internet when not in use, reducing the risk of exposure. While they offer top-tier security, hardware wallets are less user-friendly for everyday transactions and are typically recommended for long-term or large-scale cryptocurrency holdings, where security is a paramount concern.
• Advantages and disadvantages of hardware wallets.
Hardware wallets offer distinct advantages and disadvantages in the realm of cryptocurrency security. On the positive side, their primary strength lies in their unparalleled security. By storing private keys offline in a tamper-proof device, they are highly resistant to online threats, including hacking and malware attacks. This makes them an ideal choice for long-term cryptocurrency storage or safeguarding substantial holdings. Additionally, hardware wallets often support a wide range of cryptocurrencies, providing versatility for users with diverse portfolios. However, these advantages come with some trade-offs. Hardware wallets can be relatively expensive compared to software wallets, which are typically free. They are also less convenient for everyday transactions, as they require physical access to the device. Moreover, if the hardware wallet is lost or damaged without proper backup, it can result in the permanent loss of cryptocurrency assets. Therefore, while hardware wallets excel in security, users must carefully consider their specific needs and risk tolerance when deciding whether to use them.

• Recommendations for top hardware wallet brands.
When considering hardware wallet options, several reputable brands stand out for their security features and user-friendly interfaces. Ledger is a well-known choice, offering a range of hardware wallets such as the Ledger Nano S and Ledger Nano X. Known for their robust security and support for a wide array of cryptocurrencies, Ledger devices are highly regarded within the crypto community. Trezor, another trusted brand, produces hardware wallets like the Trezor Model T and Trezor One, known for their open-source nature and strong emphasis on security. KeepKey is a solid option, known for its sleek design and ease of use. All these brands provide a high level of security and support for multiple cryptocurrencies. However, it's essential to research and compare features, costs, and compatibility with your specific cryptocurrency holdings before choosing the best hardware wallet for your needs. Additionally, always purchase hardware wallets from official sources to ensure authenticity and security.


2.3 Paper Wallets
• What are paper wallets?
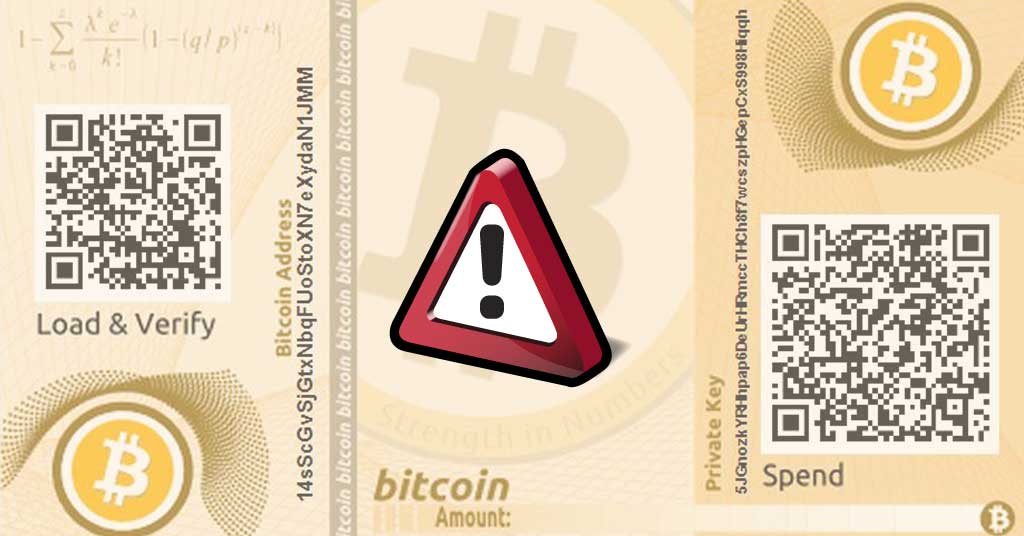
Paper wallets are a form of cold storage for cryptocurrencies, offering a secure and offline method of storing digital assets. Essentially, a paper wallet is a physical document or piece of paper that contains the public address (where funds can be received) and the private key (used to authorize transactions) of a cryptocurrency wallet. This information is usually presented as a QR code for easy scanning with a wallet application. Paper wallets are often generated using offline methods to ensure that the private key remains entirely offline and thus immune to online threats. While paper wallets are highly secure from cyberattacks, users must handle the physical document with care, as it can be lost, damaged, or exposed to potential physical threats like theft or fire. They are best suited for individuals who want to store significant amounts of cryptocurrency for the long term and are willing to take responsibility for the physical security of their wallet.

• How to create and use a paper wallet securely.
Creating and using a paper wallet securely involves several critical steps. First, generate the paper wallet offline using a trusted and secure tool or website. Ensure that the computer or device used for generation is not connected to the internet to prevent any potential exposure of the private key. Once generated, print the paper wallet on a secure and clean printer, preferably using a dedicated printer or in a secure environment to avoid potential malware or hacking. Store multiple copies of the paper wallet in safe and secure physical locations, like a safe deposit box or a fireproof safe, to protect against physical threats. Never share the private key or the associated QR code with anyone, and be cautious when using the paper wallet for transactions. When it's time to access or spend funds from the paper wallet, use a trusted software wallet to import the private key securely, complete the transaction, and then return the paper wallet to its secure storage. This approach ensures that the paper wallet remains secure while allowing users to access and use their cryptocurrency when needed.
You can navigate to the Paper Wallet section here for more info:
:max_bytes(150000):strip_icc()/Primary-Image-how-to-create-a-crypto-wallet-in-2023-7500574-3124ef4a5e634c33ab65724a686bc98a.jpg)
• Risks associated with paper wallets.
While paper wallets offer a secure method for cold storage of cryptocurrencies, they come with their own set of risks and challenges. One significant risk is physical damage or loss. Since paper wallets are physical documents, they can be susceptible to wear, tear, moisture, fire, or accidental destruction. If a paper wallet becomes illegible or is damaged, it can result in the permanent loss of the stored cryptocurrency. Additionally, paper wallets can be vulnerable to theft if not stored securely. If someone gains physical access to the paper wallet, they can easily sweep the funds by scanning the private key QR code. Users must also ensure that the computer or printer used to generate the paper wallet is free from malware or keyloggers, as any compromise of the generation process could lead to the exposure of the private key. Due to these risks, users should take extreme care in creating, storing, and using paper wallets and consider alternative cold storage options for added security.
This concludes part two of our three part series on keeping your digital coins safe and secure. Next week we will go into detail on the best practices for Crypto Wallet security, Additional Security Measures, Recovering Lost or Stolen Crypto Assets and most of all Safeguarding Your Digital Wealth.
Read Part 1:













Comments ()