FRT where innovation meets controversy. Are you concerned about privacy?
Introduction
Facial recognition is a technology capable of matching a human face from a digital image or a video frame against a database of faces to confirm an individual’s identity. Although less accurate than fingerprint recognition, it is often favoured because of its contactless nature. This technology has sparked widespread debate regarding its pros and cons. On one hand, FRT offers unprecedented advancements in security, law enforcement, and convenience, promising efficient identification processes in various sectors. However, on the other hand, concerns over privacy, accuracy, and potential misuse have ignited a growing scepticism about the ethical implications of widespread facial recognition adoption. This article will look deeper into this technology from a Cypherpunk perspective, weighing its potential benefits against the ethical and privacy considerations that have sparked a global conversation. The first article in this two part series will give a history and background of FRT and how the technology works and how it was developed and continues to develop.
What is face recognition?
Facial recognition is a clever way to verify or ascertain someone’s identity using an algorithm that processes a digital image or video frame. It picks out distinguishing features of someone’s face and matches these with the faces already logged within a database. New uses for it are being developed all the time. Digital images and video stills are becoming clearer and easier to pick out distinct people and faces, while the matching software and algorithms are getting better from increased data sources and accuracy.
The use of facial recognition and data is becoming an important part of commercial identification, helping to target individuals and personalize sales and marketing communication. It is also used in automatic image indexing, human-technology interactions, and video surveillance systems.
How Facial Recognition Works
Traditional face recognition methods, such as Voila-Jones Haar cascade or a histogram of oriented gradients, have given way to modern techniques based on convolutional neural networks (CNNs). In the face recognition process, CNNs undergo several steps:
- Face Detection: The initial step involves identifying a face within a larger image or scene. This requires distinguishing facial features from the surrounding environment and pinpointing their location within the frame.
- Face Analysis: Once a face is detected, the technology analyzes facial features, relying on the face's geometry. This analysis measures key points, known as landmarks or nodal points, including the distance between the eyes, the shape of the jawline, and the contours of the cheekbones, lips, and nose.
- Feature Extraction: The analysis results in the extraction of facial features, forming a faceprint or face template—a digital map of the face's geometry.
- Comparison: This face template is compared against a database of known faces, utilizing sophisticated matching algorithms capable of handling variations in lighting, facial expressions, and angles.
A convolutional neural network translates each face pattern into a numerical code, expressing each template as a numerical vector. The proximity of two vectors indicates the likelihood of a face match. Nodal points, representing crucial elements of facial geometry, are pivotal in creating a face template—a digital representation of unique facial characteristics.
Modern facial recognition systems employ advanced algorithms, assessing and logging over 80 nodal points from the face template. This information is transformed into a mathematical formula, termed a facial signature, encapsulating the facial features stored in the database. When encountering a new image, FRT compares the new face template to facial signatures within an existing database. With an array of artificial intelligence algorithms, the system swiftly and accurately evaluates the face template, determining if there's a match with any stored facial signature.
The continuous success of FRT relies on machine learning advancements, refining the creation and comparison of face templates and reinforcing its crucial role in security, personal authentication, and various applications in our digital ecosystem.
Applications and Use Cases of Facial Recognition
FRT has a wide range of applications worldwide – from individual onboarding and personal security to the identification of individuals in crowds and gatherings. The most common use cases of this technology include:
- Criminal identification of suspects
- Digital onboarding of clients
- Access control
- Security and surveillance
- Identity fraud prevention
- Event registrations
- Airport operations
- Financial services verification
- Smartphone unlocking
- Retail analytics
What are the benefits of Facial Recognition?
There are many benefits to FRT. A key area is improved security, both in public areas and for companies and organizations, such as banks, schools, prisons, and airports. It can help police to identify people of interest quickly and work out their movements to track them down and prevent them from causing any harm.
It can also speed up identity checks in airports, at borders, and for personal admin tasks, such as banking or entering and exiting workplaces and other buildings. It also works very well with social media, providing an alternative, non-invasive method of accessing accounts rather than inputting passwords or codes. Retailers and marketing professionals can also use the technology to tailor advertisements and commercial messages to customers more precisely.
FRT used for enforcement
FRT is already known for high speed, accuracy, and reliability. This makes it ideal for areas where quick and accurate identification is crucial for maintaining a high level of security.
For example, the US Customs and Border Protection (CBP) has committed to using facial recognition technology on 97% of international passengers by 2025. The CGP’s process involves scanning travellers with a camera that matches their live image with existing photo templates from travel documents. Once matched, they can proceed to enter or exit the United States.
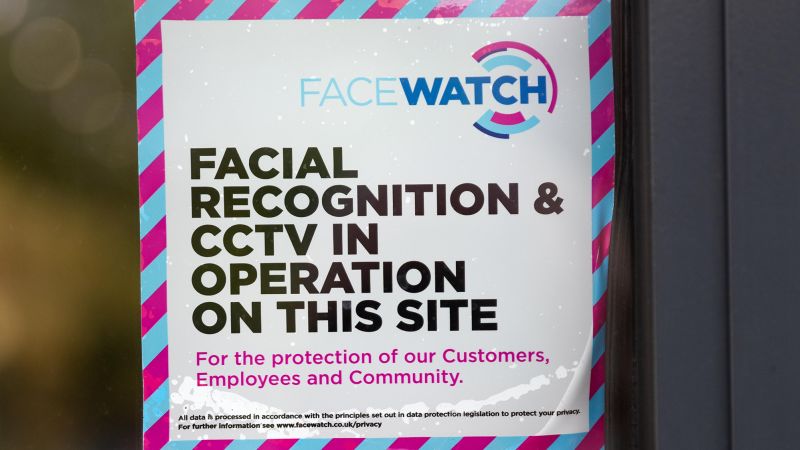
Another example is the Dubai International Airport. They use facial recognition cameras for passenger clearance, eliminating the need for passports or boarding passes. It can also be used in retail to identify known shoplifters, like the system used in certain British stores. When someone on the “shoplifter watchlist” enters the premises, artificial intelligence recognizes their face and immediately alerts security officers.
Concerns and Ethical Implications
This technology raises significant concerns related to privacy, misuse, biases, and inaccuracies. Privacy is a primary worry as the technology involves capturing and processing individuals' facial data, leading to potential breaches. Misuse concerns stem from the risk of unauthorized access or the use of facial data for malicious purposes. Moreover, biases and inaccuracies in facial recognition algorithms have been reported, with certain demographic groups facing higher error rates. These concerns underscore the importance of addressing ethical considerations and implementing safeguards to ensure responsible and fair use of FRT.
Like any technology, using FRT comes with potential drawbacks, particularly in terms of privacy and security:
- Lack of Consent: Adhering to the basic principles of data privacy laws, organizations should inform users about the collection of biometric data and obtain their consent. The primary privacy concern with FRT arises when the technology is employed to identify individuals without their explicit consent. This includes applications like real-time public surveillance or the aggregation of databases that may not be lawfully constructed.
- Unencrypted Faces: Faces are increasingly susceptible to capture from remote distances, and the cost of collecting and storing facial data is decreasing. Unlike many other types of data, faces cannot be encrypted. Data breaches involving facial recognition data heighten the risk of identity theft, stalking, and harassment, as faces, unlike passwords or credit card information, cannot be easily altered.
- Lack of Transparency: Employing FRT to identify individuals without their knowledge or consent raises significant privacy concerns, especially considering the uniqueness of biometrics. Facial scans, unlike other biometrics such as fingerprints, can be easily and remotely captured without the subject's awareness, adding an extra layer of concern.
- Technical Vulnerabilities: FRT systems may be vulnerable to spoofing attempts, where an individual masquerades as a victim using pictures or three-dimensional (3D) masks created from imagery of the victim. Additionally, FRT is susceptible to presentation attacks involving physical or digital spoofs, like masks or deep fakes.
- Inaccuracy: Another notable critique of FRT is its potential for inaccuracy. A facial scan that misidentifies someone can have enduring consequences. Moreover, accuracy levels vary by demographic, with higher false positive rates among women and people of color, potentially leading to unjust arrests in the criminal context.
Conclusion
In conclusion, this article explored FRTs history, benefits, working mechanisms, and applications. The second part of this series will shift the focus to the legal framework and regulations governing FRT, providing insights into the current state of laws and emerging regulations. Case studies will highlight successful implementations, along with controversial use cases and public reactions. Additionally, the article will discuss future trends and developments in this technology, exploring potential applications, innovations, and efforts to address ethical concerns. We will recap key points, emphasizing the importance of balancing benefits and risks. Stay tuned for an examination of the legal, societal, and technological aspects creating the future of FRT.
Relevant Articles and further reading:
- Is FRT the Perfect Tool for Oppression:

"We believe facial recognition technology is the most uniquely dangerous surveillance mechanism ever invented."
- AI facial recognition tech brings ‘airport-style security’ to UK stores, says human rights group
“We’re just here trying to prevent crime”
- The pros and cons of facial recognition technology

Facial recognition software could improperly identify someone as a criminal, resulting in an arrest, or otherwise cause them reputational damage if they were to be included on, for example, a list of shoplifters.








Comments ()